Section 1
Nothing, and Then All at Once
In 2019, Hartmut Neven, director of Google’s Quantum AI lab, observed that improvements to Google’s quantum processors were advancing at a doubly exponential rate — not just exponential like Moore’s Law, but exponential on top of exponential. Under Moore’s Law, computing power roughly doubles every two years. Under Neven’s law, the growth rate itself accelerates: four improvement cycles yield not a 16× gain (as with simple exponential growth) but a 65,000× gain. Neven described the subjective experience of this trajectory: “It looks like nothing is happening, nothing is happening, and then whoops, suddenly you’re in a different world.”
For years, quantum computers may appear to make slow progress, factoring small numbers that classical computers can already handle. Then, as multiple breakthroughs converge (better physical fidelity crosses a threshold, higher-efficiency error correcting codes, an algorithmic insight cuts resource requirements), the gap suddenly closes. What seemed like a distant threat becomes imminent within months, not years.
Whether or not Neven’s law holds precisely as a quantitative rule, or whether feedback loops from improving quantum computers result in truly non-linear growth, the qualitative pattern it describes matches the trajectory of quantum computing progress toward cryptographic relevance. Because improvements compound across multiple independent dimensions — hardware, error correction, and algorithms — progress will not be gradual and predictable. Instead, it will follow this “nothing-and-then-all-at-once” trajectory.
This sensitivity to initial conditions and assumption about rate of improvements makes precise timeline predictions extremely difficult. The majority of experts estimate Q-Day (the moment a CRQC is realized) as more likely than not in 10-12 years [9]. More aggressive projections, accounting for recent acceleration, suggest 3-5 years. Given the rapid progress and positive feedback loops leading to further acceleration, the difference between these estimates is not large in terms of technological capability; a few key breakthroughs separate them.
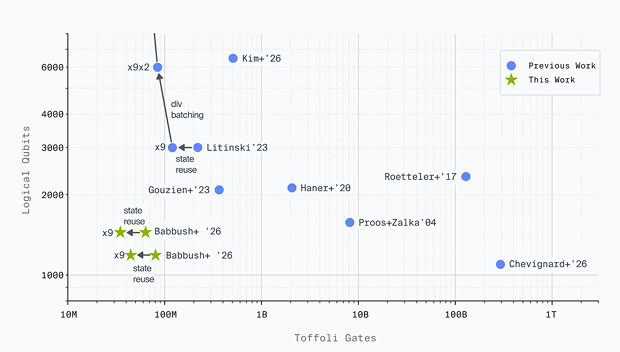
Logical Resources Required to Break 256-bit ECDLP
1. Mosca’s Inequality: A Framework for Urgency
The proper way to reason about quantum risk under timeline uncertainty is Mosca’s inequality: a framework developed by cryptographer Michele Mosca [103] for evaluating when migration must begin. If the following inequality holds, migration should already be underway:
Migration Time + Data Shelf Life > Time to CRQC
- Migration Time — The total time required to transition the system to quantum-resistant cryptography.
- Data Shelf Life — How long the data (or in blockchain terms, the assets) must remain secure. For blockchain this term is effectively infinite: UTXOs never expire and assets must be protected indefinitely.
- Time to CRQC — The remaining time before a cryptographically relevant quantum computer arrives.
If this inequality holds (if the sum of the migration timeline and the data’s required security horizon exceeds the time remaining before a CRQC exists), then migration should already be underway. Delay only widens the gap.
For blockchain systems, Mosca’s inequality is even more unforgiving. The “data shelf life” term is effectively infinite: blockchain addresses hold economic value indefinitely, UTXOs never expire, and the public keys exposed in on-chain transactions persist permanently on an immutable ledger. Bitcoin (and other digital assets) have the property that, definitionally, shelf life should be infinite — a user should always have the ability to transact with a valid key. This means the inequality collapses to an even simpler condition:
If Migration Time > Time to CRQC, the system is already compromised in expectation.
Since blockchain data is public and permanently recorded, there is no separate “harvesting” step required; the adversary’s harvest is the blockchain itself. The only question is whether the migration can be completed before a CRQC arrives to exploit it.
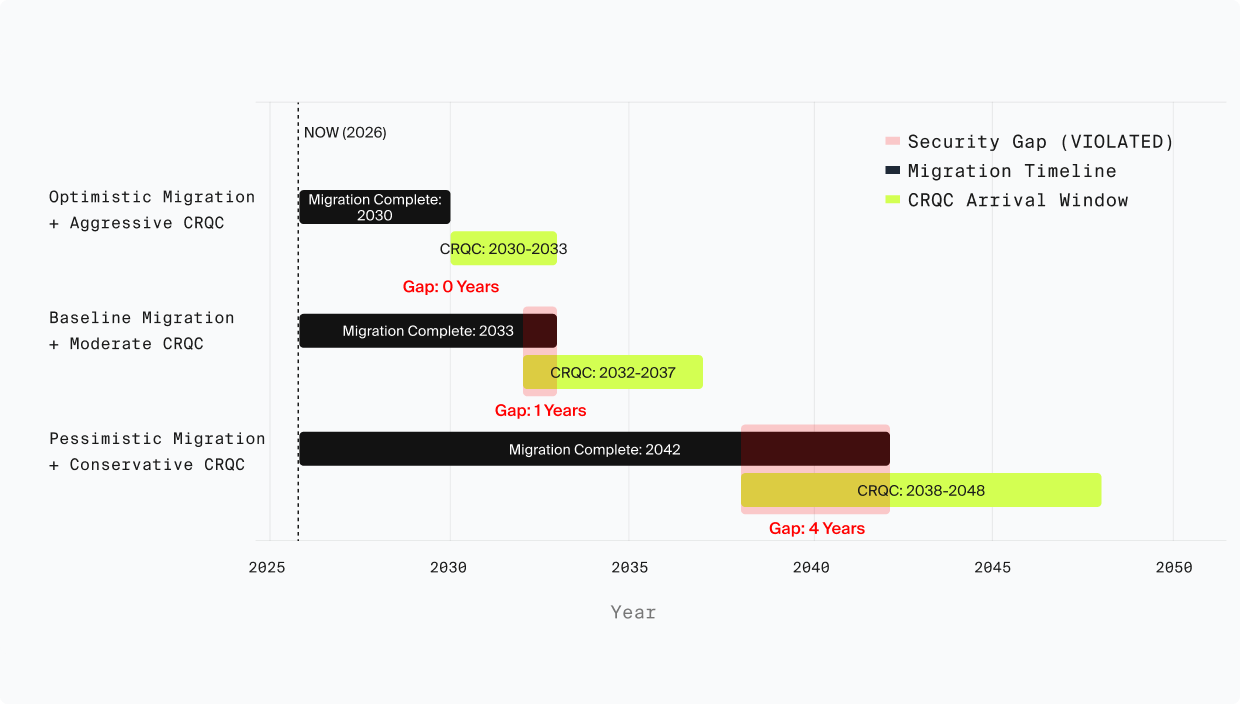
Even optimistic blockchain migration timelines extend 4–6 years from initiation, with baseline estimates of 7–13 years. Against a CRQC arrival window of 2030–2033, Mosca’s inequality is already violated under nearly all reasonable assumptions.
This is why organizations from NIST to major browser vendors are already deploying post-quantum cryptography, despite the most optimistic quantum timelines being years away. The blockchain space must adopt the same precautionary stance.
For traditional internet infrastructure, the HNDL (“Harvest Now, Decrypt Later”) threat provides the urgency: an adversary can harvest encrypted communications today and decrypt them retroactively once a CRQC arrives. This is why CISA, NSA, and NIST have jointly recommended immediate migration initiation regardless of timeline uncertainty. For data with confidentiality requirements extending beyond 2030, migration is already urgent.
Mosca's Inequality Applied to Blockchain PQC Migration
2. Timeline Uncertainty Demands Worst-Case Planning
Recent breakthroughs have drastically reduced the resource estimates for breaking 256-bit Elliptic Curve Cryptography, proving that the physical-to-logical qubit overhead is collapsing rapidly. On superconducting hardware, Google provided a zero-knowledge proof of a circuit to solve the ECDLP can be solved using between 1,200 and 1,450 logical qubits and under 90 million operations. Assuming physical error rates of 0.1%, this requires fewer than 500,000 physical qubits and takes just 18 to 23 minutes to execute. Meanwhile, neutral-atom architectures leveraging qLDPC codes can execute Shor’s algorithm for ECC-256 using approximately 10,000 to 22,000 physical qubits in as little as 5 days.
This compressed timeline introduces a critical distinction in the threat landscape based on the physical clock speeds of different quantum modalities. “Fast-clock” architectures, such as superconducting or photonic systems operating with 1-microsecond cycles, can derive a private key from an exposed public key in roughly 9 minutes. This speed enables devastating “on-spend” attacks, allowing adversaries to hijack active transactions directly from the mempool before they are recorded on the blockchain. Conversely, “slow-clock” systems like neutral atoms and ion traps operate with millisecond cycle times and are restricted to “at-rest” attacks. These slower systems will instead target dormant wallets and long-lived smart contracts where the public key has been exposed for extended periods.
“Finally, the arrival of these capabilities will likely follow a ‘nothing, and then all at once’ trajectory. Because the industry is shifting toward hiding the specific blueprints for advanced quantum attacks, the final milestones toward a CRQC will be obscured from public view — meaning Q-Day could arrive with virtually no warning.”
Highlighting this shift, researchers are now actively withholding the exact mechanics of their most advanced cryptanalytic circuits to prevent malicious use, operating under coordinated vulnerability disclosure principles. To substantiate their latest resource estimates without arming adversaries, researchers utilized zero-knowledge proofs to cryptographically verify their claims.
These topics are the focus of the next section of this report.