Section 2
Elliptic Curve Digital Signatures
The digital asset industry holds over $3 trillion in aggregate value, and virtually all of it is secured by the same class of cryptographic primitive: elliptic curve digital signatures. Bitcoin uses ECDSA over secp256k1. Ethereum uses ECDSA over secp256k1 for user accounts and BLS over BLS12-381 for consensus. Solana, Sui, Aptos, Near, and Stellar use EdDSA over Ed25519. Stablecoins, bridges, oracles, governance contracts, and custody systems all inherit the signature scheme of their host chain.
The quantum threat to digital assets is not a collection of independent, chain-specific problems. It is a single structural vulnerability — dependence on the hardness of the elliptic curve discrete logarithm problem — replicated across the entire ecosystem.
A CRQC running Shor’s algorithm reduces this problem from computationally infeasible to efficiently solvable. The result is private key recovery from any known public key. The attacker produces valid signatures indistinguishable from the legitimate owner’s, because mathematically, they hold the same key.
“The quantum threat to digital assets is not primarily about future risk. It is about present-tense exposure to a future capability.”
Two Properties That Make Blockchains Uniquely Vulnerable
Public Ledgers
Public keys, signatures, and transaction histories are permanently recorded and freely accessible. There is no "air gap" between cryptographic material and an attacker. The data a quantum attacker needs is already collected — it is the blockchain itself.
Bearer Instruments
Authorization is possession of a signing key, and signatures are final. There is no fraud department, no chargeback, no identity verification layer that can distinguish a legitimate owner from a quantum attacker holding the same private key. Once a forged signature is accepted by consensus, the transfer is irreversible.
Every major blockchain uses some variant of elliptic curve cryptography (ECC) for transaction authorization. The underlying assumption is the same: given a public key (a point on an elliptic curve), it is computationally infeasible to derive the corresponding private key. Shor’s algorithm, running on a sufficiently large quantum computer, solves this problem in polynomial time, breaking all elliptic curve schemes.
A common misconception is that hash functions like SHA-256 or Keccak-256 provide meaningful protection against quantum attacks. They do not, in the way that matters. Grover’s algorithm provides only a quadratic speedup against hash preimages, reducing 256-bit security to an effective 128 bits — far beyond practical attack. However, hash functions are not the vulnerability. The vulnerability is the signature scheme itself: the elliptic curve operation that binds a public key to a private key. If an attacker can recover the private key, they can sign any transaction they want. No amount of hash strength changes that.
Some Bitcoin addresses do benefit from hash protection where the public key has never been revealed on-chain. But this is a micro-level protection that does nothing for the macro. If a quantum adversary drains the largest exposed wallets — early miner coins, exchange reserves, or any address that has ever broadcast a transaction — the systemic damage could collapse the value of the entire network.
Common Misconceptions
Multisig does not help
If each signer uses ECDSA or EdDSA, a quantum attacker simply recovers each signer's private key independently. A 3-of-5 multisig with five quantum-vulnerable keys requires three Shor executions instead of one — a linear increase in effort, not an exponential one. The security of a multisig is capped by the weakest underlying signature scheme.
Hardware wallets do not help
A hardware wallet secures how a private key is stored and used. A quantum attacker does not need access to the device. They need only the public key, which is already on-chain. The hardware wallet is defending against the wrong threat model entirely.
“The exposure varies by chain depending on when and how public keys become visible.”
The following sections examine the specific vulnerability profiles of major blockchain ecosystems.
Bitcoin Exposure
Bitcoin’s UTXO model provides a degree of quantum protection that is real but frequently overstated. When a user receives Bitcoin to a P2PKH or P2WPKH address, only a hash of the public key appears on-chain. The public key itself is not revealed until the owner spends from that address. For outputs that have never been spent, and whose addresses have never been reused, an attacker would need to reverse a hash function to obtain the public key — which Grover’s algorithm does not make practical [16].
The protection fails under a set of conditions that cover a significant fraction of Bitcoin’s supply.
P2PK and P2MS outputs embed the full public key directly in the locking script — these include the majority of early Bitcoin coinbase transactions from 2009 to 2011. P2TR (Taproot) outputs encode an x-only public key in the address itself, making every Taproot output quantum-vulnerable from the moment it receives funds [16]. Address reuse after spending is a third vector: when a user spends from a P2PKH or P2WPKH address, the public key is revealed in the spending transaction; any new UTXOs are then secured by an exposed key [16, 17].
In a standard BIP-32 HD wallet, exposing one leaf address does not compromise sibling addresses, because each child key is derived independently [17]. However, any individual address whose public key has been revealed — whether through spending, address type, or reuse — is independently vulnerable to quantum key recovery.
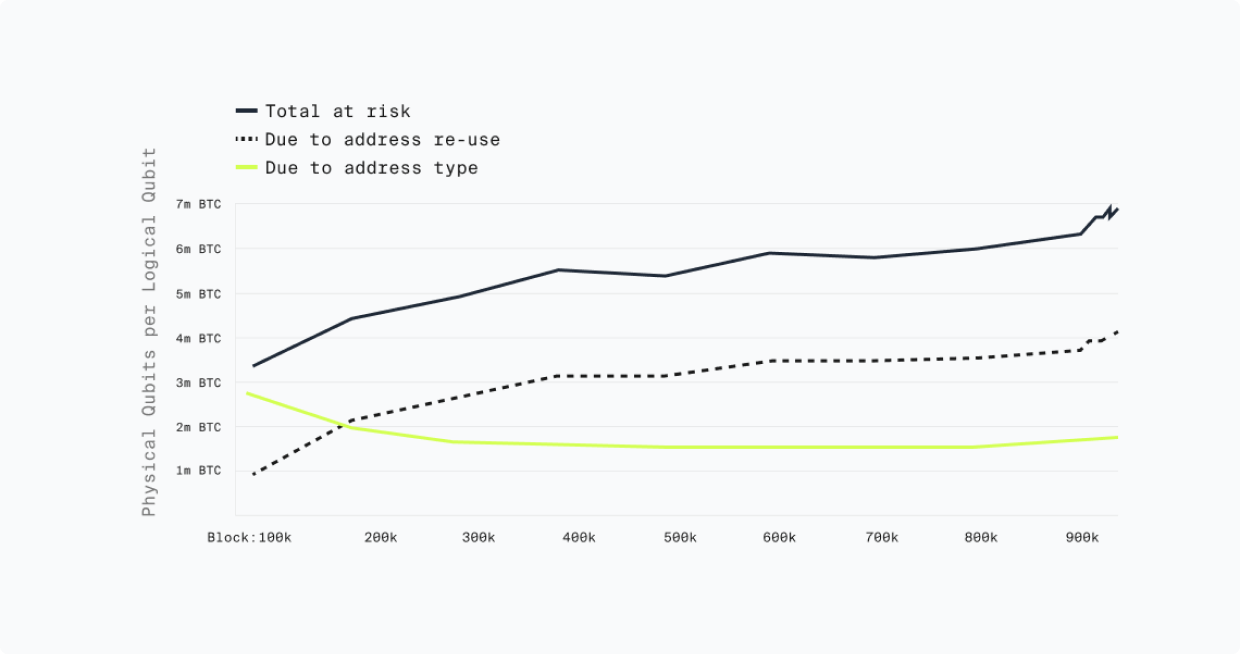
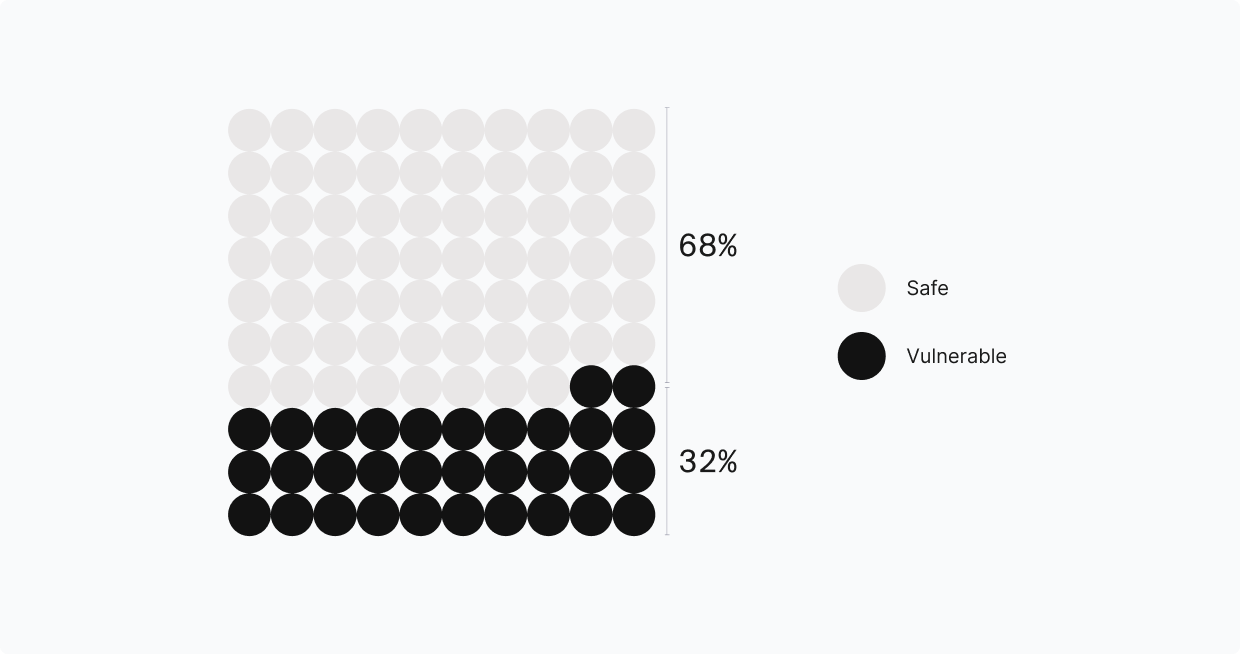
Project Eleven’s Bitcoin Risq List [18] provides a continuously updated, address-level view of quantum-vulnerable Bitcoin, categorizing every quantum-vulnerable address by the specific mechanism of exposure. As of February 2026, approximately 6.9 million BTC — roughly 33% of the total circulating supply — sits in quantum-vulnerable addresses.
Quantum-Vulnerable Bitcoin by Exposure Mechanism
| Exposure Mechanism | BTC Exposed | % Total | Notes |
|---|---|---|---|
| Address Reuse | 4,994,044 | 72.3% | |
| P2WPKH (SegWit) reuse | 1,801,410 | 26.1% | Public key via prior spend |
| P2SH (Script Hash) reuse | 1,299,221 | 18.8% | Public key via prior spend |
| P2PKH reuse | 1,202,064 | 17.4% | Public key via prior spend |
| P2WSH (SegWit Script) reuse | 691,349 | 10.0% | Public key via prior spend |
| Script Type | 1,915,211 | 27.7% | |
| P2PK (Pay-to-Public-Key) | 1,716,814 | 24.8% | Public key embedded in output |
| P2TR (Taproot) | 198,106 | 2.9% | x-only public key in address |
| P2MS (Bare Multisig) | 291 | <0.01% | Public keys embedded in output |
| Total | 6,909,255 BTC | 100% |
Source: Project Eleven Bitcoin Risq List [18], block height 936,882 (February 2026). Total across 13.9 million addresses.
Quantum Vulnerable Bitcoin — Project Eleven
Ethereum Exposure
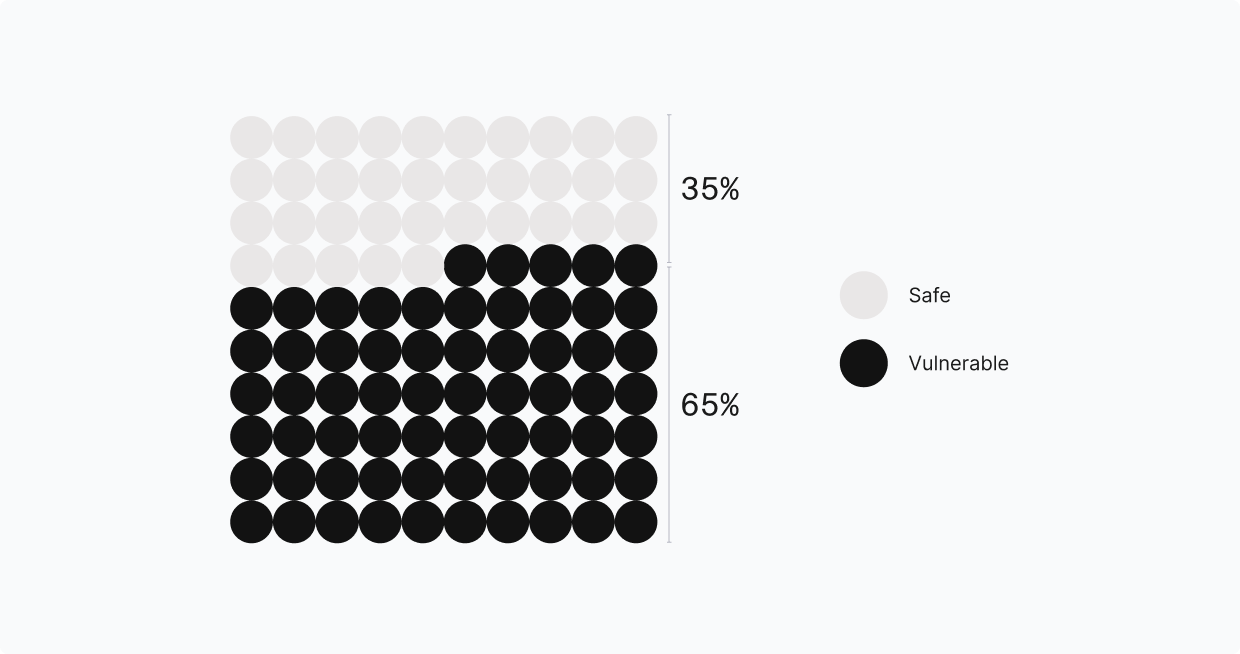
Ethereum’s account model creates broader quantum exposure than Bitcoin’s UTXO model. When an externally owned account (EOA) sends a transaction, the sender’s public key is recoverable from the ECDSA signature values (v, r, s) included in that transaction. Bitcoin can keep most value sitting behind fresh addresses; Ethereum ties value to a long-lived account, so the first outbound transaction from an address reveals the public key and that exposure persists for as long as the account remains relevant [19]. Analysis of the Ethereum blockchain has found that over 65% of all Ether is held in quantum-exposed addresses [20].
The exposure extends beyond user wallets. Ethereum’s Proof-of-Stake consensus layer depends on BLS signatures (BLS12-381), which are equally vulnerable to Shor’s algorithm [21]. Every validator’s BLS public key is published at the time of the 32 ETH deposit and remains visible in beacon chain state. A quantum attacker who recovers validator private keys could forge attestations, destabilize consensus, and trigger mass slashing. KZG commitments introduced with EIP-4844 (proto-danksharding) rely on elliptic curve pairing assumptions, adding a third quantum-vulnerable primitive to the protocol [21].
Smart contract governance introduces a distinct concentration of risk. Many of the most critical contracts in DeFi (lending protocols, DEXs, bridges, treasuries) are controlled by admin keys or small multisig wallets held by a limited set of signers. These admin keys can pause contracts, upgrade logic, change parameters, and move funds. If those keys use ECDSA and have ever signed a transaction, their public keys are recoverable. A quantum attacker does not need to find a bug in the contract code; they need only recover an admin key and call the contract’s own privileged functions [19]. The damage from a single compromised admin key can far exceed the damage from draining any individual user wallet.
Quantum Vulnerable Ethereum — Deloitte
Stablecoins Exposure
Stablecoins warrant separate treatment because they combine high systemic importance with a concentrated, privilege-key-dependent architecture that creates a distinct quantum attack profile.
The stablecoin market exceeded $300 billion in total capitalization by early 2026, with USDT and USDC together accounting for over 80% of the market [22]. Monthly on-chain transaction volume reached $1 trillion by September 2025 [23]. The passage of the GENIUS Act in 2025 established a U.S. federal regulatory framework for payment stablecoins, and integration by major payment networks has extended stablecoin rails into traditional financial infrastructure [22].
The quantum attack surface of a treasury-backed stablecoin is not only the individual user’s wallet. It is the contract’s admin keys. A quantum adversary cannot touch the actual dollars held in reserve — instead, the attack surface is purely on the liability side of the ledger: the on-chain representation of who owns what, and the privileged roles that govern it. But that is more than enough to cause chaos.
Major stablecoins are implemented as upgradeable proxy contracts where a small number of privileged addresses control the entire system [24]. The typical role hierarchy includes: the proxy admin (able to replace the contract’s entire logic), the owner (able to reassign other admin roles), a master minter role (able to authorize minters and set minting ceilings), a blacklister (able to freeze any account), and a pauser (able to halt all transfers globally) [26]. Providers most likely keep the highest-privilege roles behind multisig wallets, but nonetheless rely on ECDSA keys [26].
“This is a qualitatively different risk profile from attacking a base-layer protocol. In Bitcoin, a quantum attacker drains individual UTXOs, bounded by the exposed balance per address. In a stablecoin, a quantum attacker with admin key access can compromise the entire currency.”
Attack Scenarios
Compromised minting authority
Allows the attacker to create unbacked tokens, collapsing the peg.
Compromised blacklister key
Enables selective freezing of exchange hot wallets or DeFi vaults.
Compromised proxy admin
Allows the attacker to deploy new contract logic, potentially rewriting balances across the entire token supply [26].
Blast Radius
The blast radius extends to every protocol that holds or prices against that stablecoin: DeFi lending pools, DEX liquidity, cross-chain bridges, and the traditional financial institutions that have integrated stablecoin settlement [25].
Other Networks
The vulnerability pattern described above is not unique to Bitcoin and Ethereum. Every major blockchain that relies on elliptic curve signatures shares the same fundamental exposure.
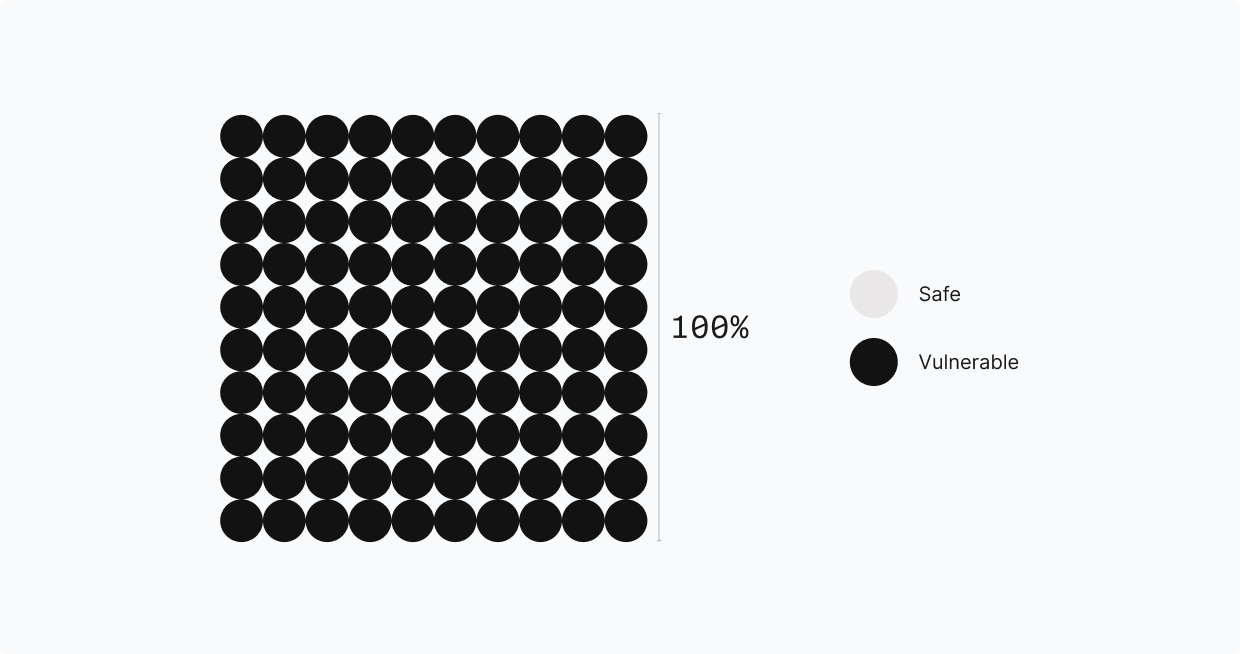
EdDSA chains — including Solana, Sui, Aptos, Near, and Stellar — use EdDSA with RFC-8032 key derivation, which computes the signing scalar from a seed via a hash function. A CRQC running Shor’s algorithm recovers the signing scalar from the public key, but cannot reverse the hash to obtain the underlying seed. This structural property has significant implications for migration that we examine in detail later in this report.
ECDSA chains generally lack this property. ECDSA chains do not define a canonical function from seed to private scalar, and wallets typically sample a random scalar directly. The signing scalar is the private key, meaning Shor’s algorithm recovers it completely with no hash-protected layer underneath.
Layer 2 networks, rollups, and application-specific chains inherit the quantum vulnerability of their parent chain’s signature scheme and add additional exposure through their own sequencer keys, fraud-proof signer sets, and bridge contracts.
The pattern is consistent across the ecosystem: every layer of the digital asset stack, from Layer 1 consensus to Layer 2 rollups to the bridges and oracles connecting them, depends on the same class of quantum-vulnerable cryptographic primitive. The only path to securing any of it is migrating to cryptography that a quantum computer cannot break. That is the subject of the next section.
“The only path to securing any of it is migrating to cryptography that a quantum computer cannot break.”
Quantum Vulnerable Solana — Project Eleven
BTC at Risk Over Time